Unified Security. Limitless Possibilities.
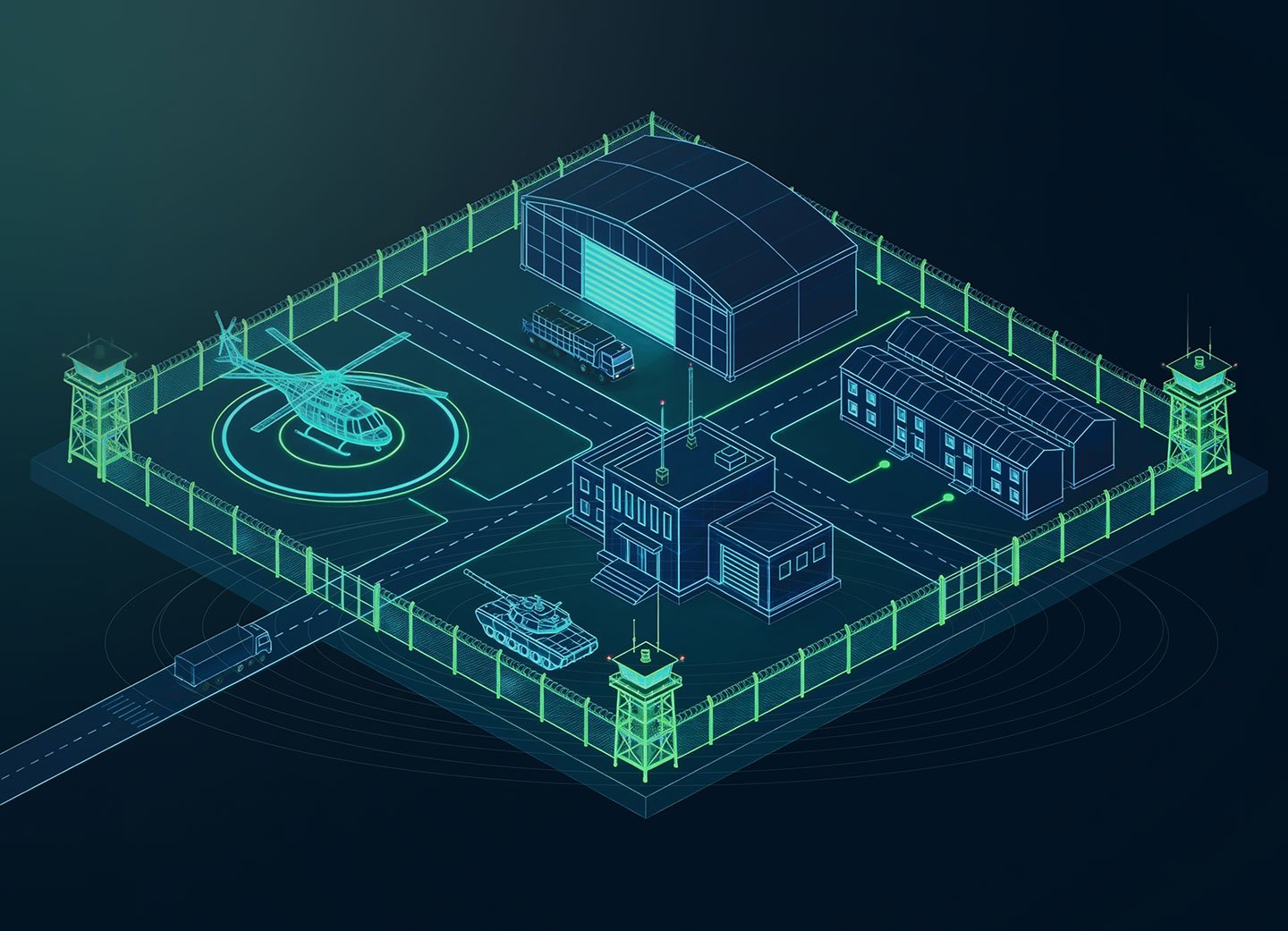
Experience what Hirsch showcased at ISC West 2026, our unified security offering connecting perimeter to core in one intelligent ecosystem.
In Las Vegas, Hirsch introduced a new approach to unified security — one that connects every layer of protection into a single, intelligent ecosystem. From perimeter detection to identity-driven access, Velocity One brings clarity to complex environments and enables faster, more confident decision-making.
• 45+ years of federal-grade security expertise •
• Trusted across critical infrastructure and regulated environments •
• Designed for complex, multi-site operations •
Security shouldn’t be fragmented.
Most security environments weren’t designed, they evolved. Over time, perimeter systems were added. Access control expanded. Video platforms were upgraded. Intrusion detection and identity tools layered in.
The result? A patchwork of disconnected systems.
When these technologies operate in isolation:
-
Visibility suffers and response slows
-
Operators are forced to piece together information across multiple interfaces
-
Leadership lacks a single, reliable source of truth.
Security leaders don’t need more tools. They need greater clarity.
Unified security eliminates fragmentation and restores operational confidence from the perimeter to the core.

One Ecosystem. One View. Total Clarity.
Hirsch brings every layer of protection together, eliminating silos and centralizing security operations in one intuitive ecosystem. Instead of managing disconnected systems, teams gain:
Unified visibility across perimeter to core
Faster response with correlated intelligence
Simplified operations and stronger compliance
All backed by proven, federal-grade reliability.
Protection that starts at the edge and connects everything.
That's Velocity One.
Hirsch unifies:
- Perimeter Protection: Detect threats before they become incidents
- Physical Access Control: Secure entry without friction
- Video Intelligence: Turn surveillance into insight
- Intrusion Detection: Respond faster, with context
- Identity & Authentication: Trust who and what has access
All working together as one system.

Built for Critical Environments
Designed for government, utilities, education, healthcare, and enterprise organizations where failure isn’t an option.
.png)
Federal-Grade, People-First
Powerful security without unnecessary complexity — built to support the people who run it every day.

Unified by Design
Not stitched together. Not bolted on. Hirsch is engineered to work as one.
